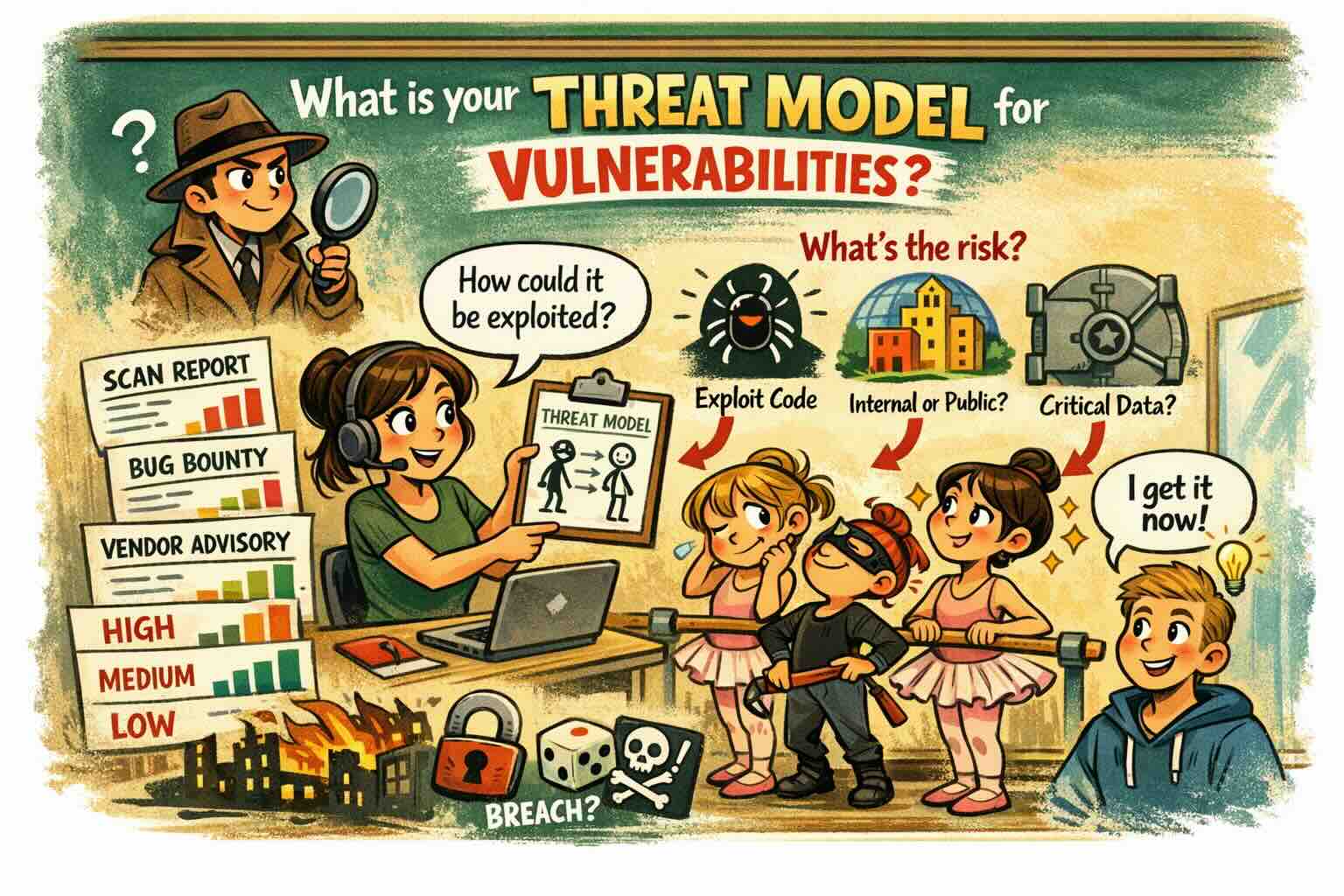
What is your Thread Model for Vulnerabilities?
One of my dear colleagues (thanks for so many questions and topics in my team!) was asking why comparing findings across tools of the same issue receives different risk ratings. So I would like to clarify and provide some pointers on exploitation and its assessment.
A short answer is: different risk models, measure different things and so impose different weightings on factors.
Risk depends on your system configuration and the systems around it, e.g., user management, firewalls, etc. Models measure specific weaknesses, not your specific environment.
On weaknesses and exploitations, there can be found several sources:
- CWE classifies types of software flaws.
It tells you what the issue is, not how dangerous it is in your system. CWE describes the weakness pattern, not the exploitability or impact.
https://cwe.mitre.org/index.html
- CVSS provides a standardized severity measurement, but it grounds on generic deployment.
It cannot know whether your instance is public, internal, or protected by compensating controls.
https://www.first.org/cvss/user-guide
- OWASP ranks classes of web risks (delivers a ranking).
It’s useful for prioritization, but it does not rate individual findings.
Factors
Two systems with the same weaknesses can have very different actual risk:
- Exposure: internet-facing vs. internal
- User base: 50 internal users vs. millions of customers
- Data sensitivity: public info vs. regulated personal data
- Controls: WAF (Web Application Firewall), segmentation, MFA (Multi-Factor Authentication), monitoring
- Business criticality: low-value tool vs. core revenue service
A CVSS 9.8 on an isolated internal lab system is not the same as a 9.8 on a public login endpoint.
This is why expert teams treat model scores as inputs, not final answers.
Evaluation Workflow
- Identify the root cause and use a baseline (CWS, CVSS or vendor score)
- Apply system context (exposure, data, users, controls, criticality)
- Derive your own risk rating
This is how two organizations will have different results. And further, there is always a spectrum, since multiple attack vectors generally yield multiple risk values.
Bottom line
Systems based on different models naturally yield risk numbers.
The actual risk depends on the overall system and will vary over time.
In a nutshell:
- Models classify.
- Scores estimate.
- Context yields final answers.
What is your procedure for assessing vulnerabilities?
References
National Vulnerability Database https://nvd.nist.gov
Vulnerability Calculator https://nvd.nist.gov/vuln-metrics/cvss/v3-calculator
MITRE CVE Program
https://cwe.mitre.org
CVSS (FIRST)
https://www.first.org/cvss
OWASP Top 10
https://owasp.org/www-project-top-ten